A Personal Data Processing Activity refers to any operation performed on personal data such as collection, storage, usage, sharing, or deletion within an organization under the Digital Personal Data Protection Act 2023. Identifying these activities is essential for DPDP Compliance, risk control, and governance. This guide explains how to identify, classify, and manage Personal Data Processing effectively across your organization.
What Is a Personal Data Processing Activity?
A Personal Data Processing Activity is any action taken on personal data across its lifecycle, forming the foundation of DPDP Compliance and governance.
Key Components of Personal Data Processing
- Collection of personal data from users, employees, or vendors
- Storage in databases, SaaS platforms, or physical records
- Usage for operations such as onboarding, support, or analytics
- Sharing with third parties or processors
- Updating, modifying, or correcting records
- Deletion or anonymization after purpose completion
Every Personal Data Processing Activity represents a control point missing even one can create gaps in DPDP Compliance.
Read also: 8 Powerful Ways to Improve Data Security and Strengthen Compliance
Why Identifying Data Processing Activities Is Important for DPDP Compliance?
Identifying each Personal Data Processing Activity ensures lawful handling of data, strengthens governance, and directly supports DPDP Compliance requirements.
Key Benefits
- Enables complete visibility into Personal Data Processing
- Reduces unnecessary or excessive data collection
- Helps manage third-party risks effectively
- Supports faster incident response and reporting
- Improves accountability across teams
- Strengthens internal governance frameworks
Read also: DPDP Data Minimization
What are the Types of data processing activities in DPDP compliance?
Different types of Personal Data Processing Activity exist depending on how data is handled throughout operations.
Types of Processing Activities
| Type | Description | Example |
|---|---|---|
| Collection | Gathering personal data | Signup forms |
| Storage | Saving data in systems | CRM |
| Usage | Operational use | Email campaigns |
| Sharing | Data transfer | Vendors |
| Modification | Updating data | Profile edits |
| Deletion | Removing data | Account closure |
Additional Classification
- Operational Personal Data Processing (HR, CRM, finance)
- Marketing-related processing activities
- Compliance-driven processing (audit logs, legal records)
- Security monitoring and fraud detection
- Vendor-based Personal Data Processing
- Automated decision-making systems
Categorizing each of these activities helps prioritize risk-heavy areas like third-party sharing
Read a lso: Simplifying DPDP Compliance: The Power of a Privacy Maturity Report
Six Essential Stages of Personal Data Processing Activities in Organizations
Six Stages Explained
- Data Collection: Data collection involves gathering relevant information from various sources to serve a specific purpose while ensuring accuracy and compliance with privacy laws.
- Data Storage: Data storage refers to securely saving collected data in structured or unstructured formats, ensuring it remains accessible for future use.
- Data Usage: Data usage is the process of analyzing, processing, and applying data to generate insights, support decision-making, or meet specific organizational needs.
- Data Sharing: Data sharing involves distributing data to internal or external parties in a controlled manner, ensuring transparency and compliance with agreements and regulations.
- Data Retention: Data retention refers to maintaining data for a defined period based on legal, regulatory, or operational requirements before considering its disposal.
- Data Deletion: Data deletion is the permanent removal of data when it is no longer necessary, ensuring it is securely erased to prevent unauthorized access.
Read more: Data Discovery Under the DPDP Act
How to Identify Personal Data Processing Activities (Step-by-Step)
Identifying a Personal Data Processing Activity requires systematic mapping of data flows, systems, and stakeholders.
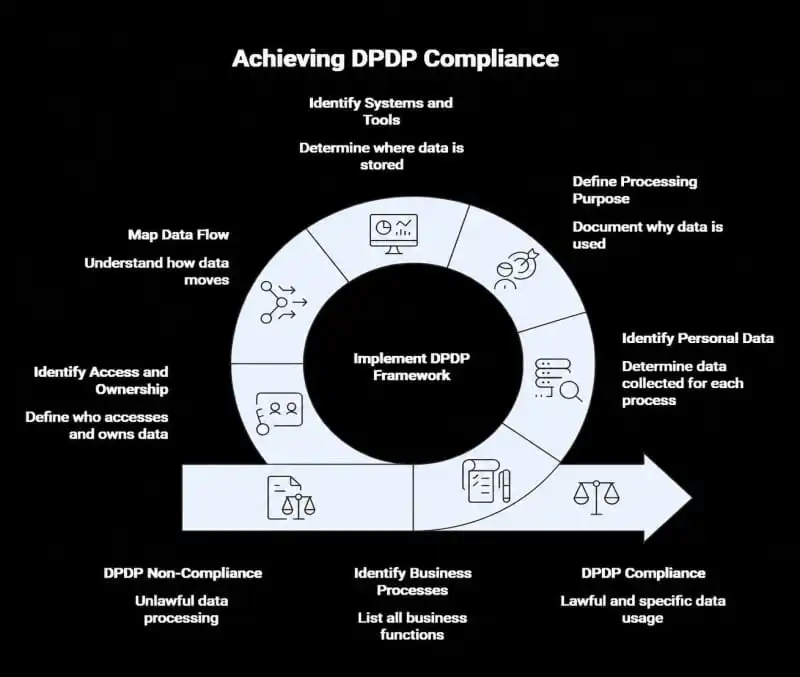
Step 1: Identify Business Processes
Start by listing all business functions such as:
- Customer onboarding
- Marketing and sales
- HR and payroll
- Finance and billing
- Customer support
Each function typically represents one or more processing activities.
Step 2: Identify Personal Data Collected
For each process, identify what personal data is collected.
Common data types:
- Name, email, phone number
- Identification details
- Financial or payroll data
- Behavioral and tracking data
Step 3: Define the Purpose of Processing
Clearly document why the data is being used.
Examples:
- Customer onboarding
- Payment processing
- Employee management
- Marketing campaigns
Purpose is critical because DPDP requires lawful and specific usage.
Step 4: Identify Systems and Tools
Determine where data is stored or processed.
Typical systems:
- CRM platforms
- SaaS tools
- Cloud storage
- Internal databases
- Spreadsheets and documents
Step 5: Map Data Flow
Understand how data moves across:
- Systems
- Teams
- Vendors and third parties
This helps identify risks and dependencies.
Step 6: Identify Access and Ownership
Define:
- Who has access
- Who owns the data
- Who is responsible for managing it
This ensures accountability and control.
Read also: What Is Personal Data Under the DPDP Act?
How Data Inventory and Mapping Help Identify Processing Activities
A strong data inventory and mapping process enables accurate identification
How They Help
- Discover all personal data across systems
- Track Personal Data Processing flows
- Identify hidden or shadow data
- Link data to business processes
- Highlight redundant data collection
- Improve reporting for DPDP Compliance
Without a data inventory, identifying processing activities becomes guesswork leading to compliance gaps.
Read more: How Modern Discovery Tools Strengthen Privacy Programs
What Are Real Examples of Personal Data Processing Activities?
Examples Across Departments
- Collecting user emails for newsletters
- Storing employee data in HR systems
- Sharing customer data with payment gateways
- Tracking user behavior via analytics tools
- Processing KYC data in financial services
- Managing support tickets with personal data
Read also: A Complete Guide to Common Vulnerabilities and Exposures
What Are Common Mistakes in Identifying Personal Data Processing Activities?
Organizations often miss critical processing activities due to incomplete visibility or poor documentation. Common Mistakes
- Ignoring third-party processing activities
- Missing shadow IT systems
- Not updating records regularly
- Overlooking offline data sources
- Failing to map data flow end-to-end
- Treating compliance as one-time activity
Most companies underestimate how much personal data they actually process.
Tools That Help Identify Processing Activities
Specialized tools automate discovery, mapping, and documentation of processing activities.
Types of Tools
- Data discovery tools
- Data mapping platforms
- Privacy management software
- Consent management systems
- Vendor risk tools
- Compliance dashboards
Manual tracking doesn't scale automation is essential for growing organizations.
Read also: 11 Steps to Jumpstart Your DPDP Compliance Program
Conclusion
A continuous, structured approach is required to manage every Personal Data Processing Activity effectively and maintain DPDP Compliance. Compliance is not about documentation it's about visibility, control, and accountability over data flows.
Final Recommendations
- Build a centralized data inventory
- Continuously update processing records
- Automate discovery processes
- Train teams on data handling
- Conduct regular audits
- Align operations with compliance requirements
To take your learning to the next level, explore our diverse selection of courses designed to help you grow professionally. Visit our Courses page to find the perfect course for your needs.
If you have any questions or need more information, our Contact Us page is the best place to reach out.
Start your journey today with Securetain, where we support your path to success.
FAQs
A personal data processing activity involves any operation performed on personal data, such as collection, storage, usage, sharing, or deletion, either manually or through automated means.
Identifying processing activities is essential for ensuring compliance with data protection laws, managing risks, and protecting individuals' privacy rights.
Skills required for personal data processing include knowledge of data protection regulations, data analysis, information security, and familiarity with privacy management tools.
The first step is to map out the data flow within the organization by identifying where personal data is collected, stored, processed, and shared.
Data processing activities can be identified through audits, reviewing data processing records, and consulting with departments that handle personal data.
Tools like data mapping software, privacy management platforms, and risk assessment tools help identify, document, and manage data processing activities.
Want to operationalize this into your DPDP program?
Talk with our team to map safeguards to evidence, owners, and ongoing monitoring - so your privacy posture holds up during audits.
Related reads
Keep exploring
 DPDP
DPDPLearn why data inventory for DPDP compliance is mandatory - discover personal data locations in databases, SaaS, HR systems & cloud. Complete guide to mapping, tools & audit...
 DPDP
DPDPComplete DPDP DPIA guide – definition, when required, step-by-step process, templates & tools for Indian businesses. Master Data Protection Impact Assessments for high-risk...
 DPDP Data Discovery
DPDP Data DiscoveryDiscover core data discovery processes under India's DPDP Act – identify personal data in databases, SaaS, HR systems & more. Essential guide to compliance, mapping, tools &...
